Keynote Speakers & Invited Talks
Below are the keynote speakers confirmed for IEEE ICCWS 2021 conference
 Professor Dr. Hafiz Malik
Professor Dr. Hafiz Malik
Professor of Electrical and Computer Engineering (ECE) at the University of Michigan – Dearborn
Talk Title: Cyber security for Connected and Autonomous Vehicles: Challenges and Solutions
Timings: 12:15 PM - 1:00 PM (23rd Nov 2021)
Abstract: Fully connected autonomous vehicles hold the promise to improve road safety and offer new mobility options to millions of people. As vehicles get smarter, cybersecurity in the automotive industry is becoming an increasing concern. Fully connected autonomous vehicles are more vulnerable than ever to hacking and data theft. This is due to the fact that automotive industry still rely on the legacy controller area network (CAN) protocol for in-vehicle control networks. The CAN protocol lacks basic security features such as message authentication, which makes it vulnerable to a wide array of attack vectors including man-in-the-middle and packet spoofing. In recent years, several researchers have successfully exploited these vulnerabilities. As, vehicle-centric technologies are expected to grow so are the associated attack surfaces. Therefore, there is an urgent need for developing robust and reliable tools and techniques for source identification and integrity verification of CAN packets. Existing solutions for CAN protocol security are limited in their ability and scope as they are unable to link received packet to the source (e.g., transmitting) ECU. This talk will provide an overview of growing attack surfaces for connected autonomous vehicles, emerging security threats, and existing solutions to mitigate them. This talk will present robust, computationally efficient, and practical solutions to message authentication problem for in-vehicle networks (IVN) including CAN. Specifically, this talk will discuss a new method based on physical attributes of CAN signals for linking IVN packets to transmitting ECU. It will also propose a layered-framework for design and development of intrusion detection and prevention system (IDPS) for connected vehicles and evaluate effectiveness of the proposed solutions
Bio: Hafiz Malik is Professor of Electrical and Computer Engineering (ECE) at the University of Michigan –Dearborn. Leading national and international sponsors have funded his research in the areas of automotive cybersecurity, cyber-physical system security, sensor security, deepfake detection, multimedia forensics, steganography/steganalysis, information hiding, pattern recognition, and information fusion. He has published over 100 articles in leading peer-reviewed journals, conferences, and workshops. He is a founding member and chief operating officer (COO) of the Global Foundation for Cyber Studies and Research, a founding member of the Cybersecurity Center for Research, Education, and Outreach at UM-Dearborn and member of leadership circle for the Dearborn Artificial Intelligence Research Center at UM-Dearborn. He is also a member of the Scientific and Industrial Advisory Board (SIAB) of the National Center of Cyber Security Pakistan. He is a member of MCity Working Group on Cybersecurity, since 2015.
 Dr. Zahri Yunos
Dr. Zahri Yunos
Chief Operating Officer of CyberSecurity Malaysia under the Ministry of Communications and Multimedia
Talk Title (Online): APT Malware Threat: Case Studies In Malaysia
Timings: 2:00 PM- 2:45 PM (23rd Nov 2021)
Abstract: Issues on network security have escalated ever since the Internet was introduced. Many researchers have intensified their efforts to ensure that security threats are discovered and mitigated in a well-timed manner. Today, cyber criminals have introduced sophistication in their attack techniques that makes the traditional way of safeguarding the enterprise networks are not effective. CyberSecurity Malaysia has developed a ‘LebahNET’ project, a computer security device evasive attacks detection based on honeypot distributed computer security mechanism. In addition, CyberSecurity Malaysia has developed a Coordinated Malware Eradication & Remediation Platform project, a system that able to detect and mitigate cyber threat with identifying unknown malware threats, preventing data breaches and preventing wide malware infection. These projects help in understanding and mitigating unknown malware threats.
Bio: Dr. Zahri Yunos is the Chief Operating Officer of CyberSecurity Malaysia, an agency under the Ministry of Communications and Multimedia Malaysia. Dr. Zahri is a central figure in establishment of the OIC Computer Emergency Response Team (OIC-CERT), a collaborative effort of cybersecurity initiatives amongst the OIC countries. Dr. Zahri holds a PhD in Information Security from the University Teknikal Malaysia Melaka, Malaysia. He has been appointed as Adjunct Professor at several local universities in Malaysia. He also has been appointed as industry adviser to several research institutions in Malaysia and abroad. He has contributed to various publications and presentations on topic related to cyber security, business continuity management and cyber terrorism.
 Professor Dr. Awais Rashid
Professor Dr. Awais Rashid
Professor of Cyber Security at University of Bristol
Talk Title (Online): Developing a programme of research on privacy, harm reduction and adversarial influence online: The REPHRAIN Centre
Timings: 2:45 PM- 3:30 PM (23rd Nov 2021)Abstract: Digital technologies pervade our daily lives and bring many benefits through delivering of online services to billions of users globally. However, alongside the many positive benefits of such a data-driven digital economy, serious challenges – e.g., privacy violations, micro-targeting of individuals, online abuse/victimisation, fraud, disinformation – have emerged. With innovations such as smart cities, IoT and mobile connectivity leading to further growth in connected digital platforms a nd services, we must consider a holistic programme of research to anticipate and address issues of privacy and online harms. In this talk, I will discuss the programme of research — being undertaken within the REPHRAIN centre — to deliver interdisciplinary research drawing upon social and technical sciences to advance state-of-the-art in privacy enhancing technologies and online harm mitigation approaches.
Bio: Awais Rashid is Professor of Cyber Security at University of Bristol where he heads the Cyber Security Group and is Director of the EPSRC Centre for Doctoral Training in Trust, Identity, Privacy and Security in Large-Scale Infrastructures. He is also Director of the National Research Centre on Privacy, Harm Reduction and Adversarial Influence Online (REPHRAIN). His research interests are in security of cyber-physical systems, software security and human factors. He leads projects as part of the UK Research Institute on Trustworthy Industrial Control Systems (RITICS), UK Research Institute on Sociotechnical Cyber Security (RISCS, National Centre of Excellence in Cyber Security of IoT (PETRAS) and the ESRC Digital Security by Design Hub+ (Discribe). He also leads CyBOK: an international effort on developing a Cyber Security Body of Knowledge to provide interdisciplinary foundations for education and training programmes.
 Dr. Salman Baset
Dr. Salman Baset
Product Security, MongoDB, USA
Talk Title (Online): State of Cloud Security, and its Future
Timings: 9:15 AM - 10:00 AM (24th Nov 2021)Bio: Dr. Salman Baset drives the security and compliance product management for MongoDB Cloud and database. At MongoDB, he has led numerous products and features to fruition, including MongoDB Atlas for Government. He has worked at IBM and IBM Research, as CTO Security of IBM Blockchain Solutions, and as a Research Staff Member. He has co-authored over 30 papers and has over 25 patents, issued or filed
 Mr. Razi Bin Rais
Mr. Razi Bin Rais
Senior Technical Program Manager, Microsoft Identity Engineering, USA
Talk Title (Online): Zero Trust Security: What it is and why it’s important to embrace it to battle cyberattacks
Timings: 10:00 AM- 10:45 AM (24th Nov 2021)Abstract: As cyberattacks became sophisticated and prevalent across the globe, private organizations and governments alike must adopt a new security model that is effective against wide variety of attacks while embracing the mobile remote workforce. A new security model based on “Zero Trust” strategy is key to securing data, systems, and services. In 2021, United States White House issued an executive order mandating all federal agencies to adopt Zero Trust on urgent basis. Cloud providers like Microsoft, Google, Amazon, Alibaba have also made Zero Trust critical part of part of their security strategy. This session will explore key tenets and principles of the Zero Trust model and how it can be leveraged to improve the security posture of an organization.
Bio: Razi Rais is a Senior Technical Program Manager in Microsofts Identity engineering team in New York where he is focusing on Cybersecurity.Over the past 16 years he has worked across the globe including Asia, Middle East, and Europe. Throughout his career, he has held a variety of roles including software engineer, architect, trainer, and a visiting professor. He likes to engage with the community through writing and speaking. He has co-authored two books on the topic of cloud computing. He is also a member of IACR and OWASP security communities. He can be reached online via LinkedIn.
 Professor Zoltan Rajnai
Professor Zoltan Rajnai
National Cyber Coordinator of Hungary; Professor, Obuda University – Hungary
Talk Title: National cybersecurity challenges, coordination and cyber protection of critical infrastructure in Hungary
Timings: 12:15 PM- 1:00 PM (24th Nov 2021)Abstract: In modern democracies the digital revolution has been stretching to all aspects of life which generates significant dependency. Nowadays members of the society are less viable if they do not use e-mail addresses, bank accounts and cards, or some sort of positioning system. The role and significance of digital infrastructures is undisputed, they became unquestionable components of transparent state functions, economic prosperity, and successful scientific research. One the one hand, modern information society considers information and communication technologies the engine of societal evolution. On the other hand, the challenges of dependency, the dynamics of development and the rate of penetration involve serious threats. Nowadays, all countries rely on the latest technologies to drive economic and social growth, and to make their most critical infrastructure systems operating smoothly. We all live in a digital landscape full of cyber threats and vulnerabilities. In the future both public and private sector cybersecurity professionals must be highly collaborative and interconnected to fight against cyber threats. To exchange information and share best practices about cyberspace issues and the resulting threats, is a good start to enhance cooperation and create trust between countries facing the same challenges to ensure the resiliency of critical infrastructure in the future. Evolving threats will continue. Users’ awareness, training and education are the cornerstones of critical infrastructure cybersecurity. The speaker’s presentation will highlight some issues of the Hungarian aspects of national cyber security.
Bio: Professor Dr. Zoltán Rajnai is currently the National Cyber Coordinator of Hungary and professor at the Obuda University. Previously Dr. Rajnai served as Colonel in Hungarian Defense Forces (1981-2013) and was professor at the National Defense University in the field of Information, info-communication, and telecommunication systems (1993-2013). Since 2015, Dr. Rajnai also is the Dean of faculty of Mechanical and Safety Engineering, Head of Doctoral School on Safety and Security Sciences with main responsibilities in the field of Cyber Security, Information Security, info-communication, and telecommunication systems. Dr. Rajnai received education from the High School at the Hungarian Defense Forces (1981-1985), the Military Academy (1990-1993), the Doctoral School on Military Sciences (1997-2000), and the Joint Defense College- Paris, France (2003-2004).
 Mr. Ahrar Naqvi
Mr. Ahrar Naqvi
CEO Ebryx
Talk Title: Incident Readiness and Response
Timings: 10:45 AM- 11:30 AM (24th Nov 2021)Abstract: Being well-prepared for incidents and effective incident response are key in limiting damage from incidents and minimizing recovery time. Lack of effectiveness here can lead to dire consequences. Yet most organizations tend to be ill-prepared and incident response tends to be chaotic and ill-executed, thus causing avoidable damage. The problem is especially acute in skill and resource constrained environments and extends beyond organizations to critical sectors. Market and organizational dynamics tend to compound the problem. This talk is aimed at highlighting key aspects of effective incident readiness and response and possible approaches to improving the situation in such environments.
Bio: Ahrar Naqvi is the CEO of Ebryx, a company he founded in 2008 in the US and Pakistan. Ebryx is the developer of a Zero Trust Network Access product. Its R&D services power some of the world’s leading products in network security, endpoint security and insider threat detection. Ebryx also offers security assessments, compliance, SOC, incident response and digital forensics services. Its customers include local banks, Silicon Valley tech startups and Fortune 500 companies. Before Ebryx, Ahrar was EVP Engineering at Silicon Valley based Palmchip; Chief Architect at Veraz Networks and a product architect at Oracle. Ahrar has an MS in Electrical Engineering from Stanford University.
 Professor Siraj Shaikh
Professor Siraj Shaikh
Head of System Security Group, Coventry University, UK
Talk Title (Online): Cybersecurity Challenges for Mobility and Transport Infrastructure
Timings: 2:45 PM - 3:30 PM (24th Nov 2021)Abstract: While cyber-physical systems security poses technical challenges of design and verification, problems of in-life monitoring and risk perception for effective secure operation cannot be ignored. We focus on transport and mobility platforms for the security risks they pose, and examine what the current state of the art to address such risks. The concepts presented here sit at the intersection of computer science, cybersecurity and transport engineering.
Bio: Professor Siraj Ahmed Shaikh is Professor of Systems Security at the Institute of Future Transport and Cities (IFTC) at Coventry University (UK), where he leads the Systems Security Group. He is currently the Director of Research (Interim) at IFTC. He is also Founder and Chief Scientist at CyberOwl, which is a VC-backed venture addressing cyber risk analytics for the maritime and CNI sectors. Over the past 20 years, his research interests have included threat modelling, cyber-physical systems security testing, and security policy-making. His research has been funded by EPSRC, RAEng, MoD, NCSC and Lloyds Register Foundation.
 Dr. Richard Thomas
Dr. Richard Thomas
UKRRIN - Industrial Fellow in Data Integration and Cybersecurity, University of Birmingham, UK
Talk Title (Online): The Cyber Security of Rail
Timings: 2:00 PM- 2:45 PM (24th Nov 2021)Abstract: As the critical national infrastructure continues to digitalise, safety and cyber security now co-exist. These systems are designed with typical lifespans measured in decades, meaning that they have to defend not only against current adversaries, but also emergent threats. This talk will explore the rail sector's journey in digitalisation, from traditional lineside signalling, to complex, inter-connected digital systems and how cyber security requirements and assurance are unavoidable in the digital railway, and how new legislation and regulation is driving a cyber security culture change in the EU and international sectors.
Bio: Dr Richard Thomas is an Industrial Fellow in Data Integration and Cyber Security and Rail Cyber Security Research Lead at the University of Birmingham Centre for Railway Research and Education, the lead for the UK Rail Research and Innovation Network. His Ph.D. reviewed the cybersecurity for some of the UK and European railway standards, identifying the challenges and proposing solutions to ensure future security. His research interests include the security of the ‘industrial internet-of-things’ and how we can leverage the wealth of data available from the rail sector. He also takes an interest in general cybersecurity topics including cybersecurity education and consumer issues, featuring on the BBC’s Rip Off Britain programme in mid-2018. Dr. Richard was part of the Research Institute in Threats to Industrial Control Systems and is now a member of the Research Institute in Trustworthy Interconnected Cyberphysical Systems, receiving a grant to address the challenges the rail sector faces when moving towards compliance with the EU Network and Information Systems Directive, identifying critical vulnerabilities in industrial systems, and was one of the first UK academics to be listed on Siemens' Hall of Thanks for his work on vulnerability research and disclosure
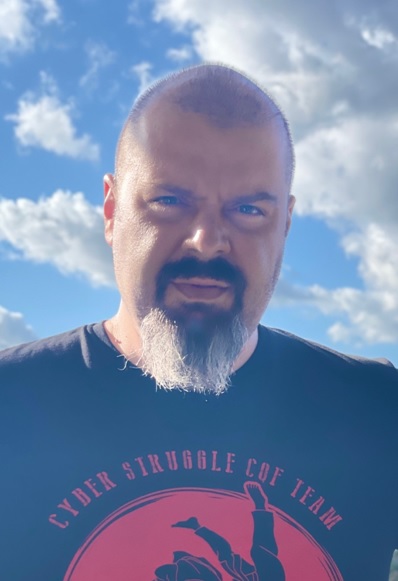 Kubilay Onur Gungor
Kubilay Onur Gungor
Cyber Struggle, Turkey
Talk Title: Warrior mindset and functional development for the irregular warfare side of the future cyber struggle
Timings: 11:00 AM- 11:30 AM (24th Nov 2021)
Abstract:
On the contrary of the definition as an additional domain to Air, Land, Sea, and Space, Cyber
is a truly irregular framework covering all other domains as well as carrying extreme uncertainty.
We do not know when the attack will occur, how long it will take, how much power will be in use,
where it will come from. Basically, we are trying to prepare ourselves to the unknown! On top of
that, there is no border between war and peace. Therefore, this phenomenon is a struggle rather
than a war, and unorthodox struggles require unorthodox approaches with teams and individuals.
Bio:
Kubilay has almost 15 years of experience in the field and has started his professional
career with cryptanalysis of image encryption algorithms using chaotic logistic maps.
After several years of penetration testing and red teaming experience in different
companies, he worked as an incident management expert in multinational companies.
He also worked at one of the biggest universities in Turkey as a lecturer for 3 years
and contributed 5 international technical cybersecurity books as a technical reviewer. As
an addition of cybersecurity, Kubilay has an extreme passion of different security topics
such as terrorism and intelligence studies, psychological warfare, war studies and their
cyber world implications. Besides technical certifications, Kubilay has MSSc in International
Relations and Terrorism as well as different terrorism related certifications, foreign policy
certification, advanced tactical shooting, operative tactical shooting, tactical combat casualt
care and survival extreme condition certifications. Currently, he is still working on
interdisciplinary cybersecurity as a researcher in Cyber Struggle.
 Mr. Taylan Esen
Mr. Taylan Esen
CTO Angora Networks, Turkey
Talk Title (Online): Security Services Chaining
Timings: 10:00 AM- 10:45 AM (24th Nov 2021)
Abstract:
Networks is the new circulatory system of the world. Everything is now irresistibly connected. From airplanes/fighter
jets to the smallest sensors in the underground, all data generation or consuming points need to be engaged to better
create a combined vision, holistic view and informed decision making. So we need to protect this environment consisting
of unlimited data access, processes and subsystems where every byte may need a different approach for the best, but
beyond that, useful security.
The goal of the presentation is to share, how different measures should be combined inside a network to provide
different level of security for distinct requirements. How to manage security services, how to monitor breaches,
leaks or even simple steps taken by users, not only for protection but also, to understand the ecosystem of
application and user. Understand how new technologies like, behavioral analysis, data mining, artificial intelligence
and others would help your network, become more secure with optimal effort, time and cost.
Bio: Mr. Taylan Esen is a computer engineer graduated from Middle East Technical University with 20 years of experience on networking and security. He worked for global companies like Cisco Systems and F5 Networks and led many big projects that creates blueprints for new technology deployments. He is currently the CTO of Angora Networks, headquartered at Turkey and focused on design, development, and manufacturing of network and security devices and software.
 Prof. Dr. Seref SAGIROGLU
Prof. Dr. Seref SAGIROGLU
Director of GAZI AI CENTER, Gazi University, Turkey
Talk Title: Data Analytics, Security and Privacy Issues in Smart Grid
Timings: 11:00 AM- 11:30 AM (24th Nov 2021)Abstract: Big data has great potential to provide opportunities not only many fields but also smart gird enhancing technical, organizational, social and economic gains and contributions. The current potential of applying big data approaches for better planning, managing, designing, and securing power grid operations are very challenging tasks and needs significant efforts. This talk will cover the issues of computational complexity, data security and privacy, cost, management, planning and integration of big data into power grid systems and also focus on the key challenges in big data analytics, privacy and security issues.Finally, some issues supported by Gazi AI Center are summarised using big data analytic laboratory infrastrature and laboratory.
Bio: Prof. Sagiroglu completed his undergraduate education in 1987 at Erciyes University, Department of Electronics Engineering. He completed his doctoral studies at the University of Wales College of Cardiff (now Cardiff University, UK) in 1994. He continues his academic career as a professor in Software Engineering at Gazi University Computer Engineering Department. Sagiroglu has organised more than 50 national and international events as chairman, co-chairman, organising committee members such as International Conference on Information Security and Cryptology (www.iscturkey.org), International Conference on Computer Science and Engineering – IEEE (www.ubmk.org), Big Data, Deep Learning and Fighting Cyber Terrorisms – IEEE (www.ibigdelft.org), IEEE International Conference on Machine Learning and Applications (www.icmla-conferences.org), Big Data Analytics, Security and Privacy Workshop (www.bigdatacenter.gazi.edu.tr), National Conference on Cyber Terrorism (www.siberteror.org), Turkey Open Data Conference (www.acikveriturkiye.org), IEEE 5G Summit-Istanbul (www.ieeesummit.org), National IPv6 Conference (www.ipv6.org), Prof. Sagiroglu has delivered as invited or keynotes peakers more than 500 seminars, talks, conferences at universities, schools, sectors, TV and Radio Programs, institutions and organisations in the topics of Information Security, Big and Open Data, Cyber Security and Defense, Artificial Intelligence, Artificial Neural Networks, Software Engineering, Privacy, Biometrics, Innovation Culture Creation, IPv6, etc.

